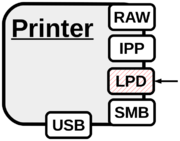
LPD
The Line Printer Daemon (LPD) protocol had originally been introduced in Berkeley Unix in the 80s. The existing implementation was later specified by RFC1179 [1]. The daemon runs on port 515/tcp and can be accessed using the ‘lpr’ command. While the LPD process was traditionally hosted on a computer system connected to the printing device, today's network printers run their own daemon directly accessible over the network. To print, the client sends a control file defining job/username and a data file containing the actual data to be printed. The input type of the data file can be set in the control file by choosing among various file formats. However it is up to the LPD implementation how to actually handle the print data. A popular LPD implementation for Unix-like operating system is LPRng [2]. LPD can be used as a carrier to deploy malicious PostScript or PJL print jobs. The protocol itself is not further analyzed in this wiki, with the exception of accounting bypasses and a fuzzer written to discover buffer overflows in LPD implementations. The lpdprint tool included in PRET is a minimalist way to print data directly to an LPD capable printer as shown below:
lpdprint.py hostname filename
→ Related articles: Fundamentals, Attack carriers, Accounting bypass, Buffer overflows
- Jump up ↑ RFC1179: Line Printer Daemon Protocol, L. McLaughlin, 1990
- Jump up ↑ LPRng – An Enhanced Printer Spooler, P. Powell